
Every network router gets its own IP address on the Internet. In a sense, your IP address is like your street address. It tells people who have it on hand or, more precisely, in their network logs, where you were when you accessed a website.
Cybersecurity professionals find IP addresses useful for a couple of processes, including traffic filtering, attacker identification, threat vector blocking, fraud prevention, an indicator of compromise (IoC) list expansion, and alert prioritization. These are discussed in greater detail below.
Table of Contents
What Is an IP Address?

img source: blog.mozilla.org
An IP address is most commonly a unique set of four numbers ranging from 0 to 255 separated by periods. Each Internet-connected device can have an IP address between 0.0.0.0 and 255.255.255.255. It is not a random number. Instead, it is produced mathematically and allocated by the Internet Assigned Numbers Authority (IANA), a division of the Internet Corporation for Assigned Names and Numbers (ICANN), the nonprofit organization that helps maintain the Internet’s security and makes it accessible to all.
IP addresses are of two major types, depending on the IP space they are part of—IPv4 or IPv6. In the early days of the Internet (way back when it had only a few users), all users were assigned IPv4 addresses (e.g., 123.45.67.89). But as the number of Internet users grew (exponentially at that), the IPv4 address space started to run out of available IP addresses. Enter IPv6, which added 340 undecillion IP addresses for the use of the ever-growing volume of Internet-connected devices.
Types of IP Addresses
Apart from being categorized as either an IPv4 or IPv6 address, IP addresses can also fall under these three categories:
-
Dynamic
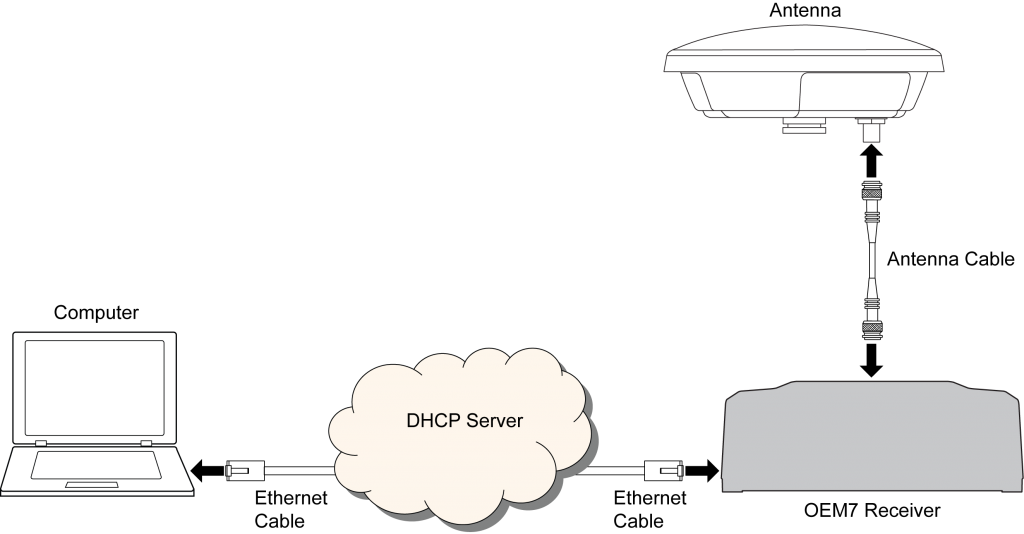
img source: docs.novatel.com
This type of IP address changes automatically and regularly. Each ISP typically has tons of IP addresses, which they assign to customers. All dynamic IP addresses are periodically reassigned so the ISP can save money. Instead of buying additional IP addresses each time it runs out of available ones, it simply recycles those that former subscribers no longer use to new customers. Sometimes, ISPs change clients’ IP addresses to make it harder for cybercriminals to hack into customers’ networks.
-
Static
This type of IP address doesn’t change. Companies that run and maintain their own servers typically use static IP addresses to ensure their websites and email addresses have consistent IP addresses. That way, anyone who wants to locate them on the Web will always be able to.
-
Reserved

img source: ciklotron.net
This type of IP address is strictly for private use. That means the devices that use them can’t be accessed outside the networks they are connected to.
How Can IP Address Identification Help with Cybersecurity?
Cybersecurity investigators and law enforcement agents can use IP addresses to track down attack perpetrators and sources. The six cybersecurity processes below describe how in more detail.
1. Traffic Filtering

img source: plixer.com
It has become increasingly popular for various cybersecurity outfits to identify cybercrime or attack hotspots to help individuals and companies protect their data, assets, and infrastructure from all kinds of threats. An example would be the Spamhaus Project’s regularly updated list of 10 worst spam countries.
Integrating an IP geolocation tool into your existing systems to keep out or at least monitor devices that come from known cybercrime or attack hotspots (aka traffic filtering) can lessen your network’s chances of getting compromised. For instance, if the IP address 222[.]186[.]30[.]76 (from one of the top 2 spamming countries China) keeps appearing in your network logs, you can investigate it and most likely find that it is a confirmed malicious IP address by AbuseIPDB. Setting up alerts each time IP addresses from the listed countries access your systems can reduce your chances of becoming a cyberattack victim.
2. Attacker Identification

img source: swift.com
When a network or system gets breached, the first thing an administrator does is to look at the logs. That would show what websites or devices communicate with the affected device when the infiltration is suspected to have occurred. These sites and systems are often identified by either domains or IP addresses.
If the computer’s last user, for instance, downloading a file from a page identified by the IP address 50[.]17[.]5[.]224, you can use an IP geolocation tool or database like this one to learn more about its owner. IP geolocation would tell you that the IP address owner is from the U.S., specifically Ashburn, Virginia, and more. The information could serve as a starting point for a more in-depth investigation on whoever is behind the attack.
3. Threat Vector Blocking
Security vendors often publicize malicious IP addresses in their blogs and other threat platforms to warn users about the risks of accessing them. The users are advised to prevent these dangerous web properties from communicating with and compromising their systems.
IP blocklists like AbuseIPDB updates its list of malicious IP addresses daily, for instance, to name the IP addresses that users should avoid at all costs. Network administrators can include the malicious IP addresses in the network blacklist so no form of communication going to and coming from the malicious servers or computers can get through.
4. Fraud Prevention

img source: completecontroller.com
The security teams of e-commerce companies can also benefit a lot from using an IP geolocation tool. Geolocation data can help them verify customers’ identities during transactions.
If a client with the New York City, U.S., IP address 72[.]229[.]28[.]185, for instance, suddenly makes a huge purchase coming from 94[.]158[.]96[.]2, IP geolocation will tell you that the user is in Moscow, Russia. Before letting the transaction through, therefore, you can make a quick phone call to the customer to confirm the purchase. That should prevent your client from getting defrauded if he/she isn’t the one behind the transaction.
5. IoC List Expansion
While publicly available IoC lists are indeed helpful in preventing threats from getting into your network, they’re not always as extensive as they can be. But they can serve as good starting points to determine other potential threat entry points that may need to be blocked as well.
Malicious IP addresses identified as IoCs can be subjected to reverse IP/DNS lookups to identify other domains that may be connected to an ongoing attack.
6. Alert Prioritization

img source: liang-tong.me
Alert fatigue is a problem for most companies. But it is avoidable if their security teams can prioritize alerts. An IP geolocation tool can help with that.
Instead of analyzing thousands of suspicious IP addresses a day, for instance, you can reduce this number by focusing on those originating from the top cybercrime hotspots identified in security reports. To avoid spam with malicious attachments or links, you can prioritize looking into communications coming from IP addresses based in the top spamming countries.
IP addresses, whose owners can be identified with the help of IP geolocation, are useful data points for a variety of cybersecurity processes. Not only can it reveal attack perpetrators and sources but also prevent fraud and more.







